This post explains how to set up WordPress to use SSL and load all pages with HTTPS URLs. We’ll show you how to fix “mixed content” type errors that may come up when a page served over HTTPS links to non-HTTPS content.
Your WordPress Site Should Use SSL
Setting WordPress to use an SSL certificate to serve pages over HTTPS doesn’t make you 100% secure against all of the kinds of attacks that can befall a website, but it should be done on nearly every site using Paid Memberships Pro.
The use of an SSL certificate is required by the PCI Security Standards Council on any site accepting credit cards [more] and is required by most gateways even if the checkout is completed “offsite”.
Search engines like Google also penalize the search rankings of sites without SSL certificates and web browsers like Chrome are now showing more severe warnings on pages with password or credit card fields if an SSL certificate is not active.
So, how do you setup your WordPress site to always use HTTPS/SSL?
Step 1. Backup Everything
Before you get started, perform a full backup of your website. The steps outlined in this tutorial touch on your WordPress files, database, and even maybe your server configuration. So be sure to back up your website at all levels: files, database, and server configuration.
Step 2. Make Sure You Have an SSL Certificate
If you don’t already have an SSL Certificate—or you aren’t sure if your do—ask your host. Purchasing and getting your host to install your SSL is the easiest (and often free!) way to get an SSL Certificate.
The details and cost of this are different for each host, but they will know exactly how to get your WordPress site to use SSL and the HTTPS protocol. We have a complete guide on how to install your SSL certificate with both the “easy” and advanced steps.
View our full guide on How to Install Your SSL Certificate for more help obtaining an SSL »
Step 3. Tell WordPress Your Site URL is HTTPS://…
Once you have your SSL certificate installed on your WordPress site’s web server, you have to actually change your WordPress site’s home_url to the https:// version.
Use the Really Simple SSL Plugin
We recommend using a really simple plugin called Really Simple SSL, a free and open source plugin just like Paid Memberships Pro available in the WordPress.org repository.
Really Simple SSL automatically detects your settings and configures your website to run over HTTPS. To keep it lightweight, we kept the options to a minimum. Your website will move to SSL with one click.
—via WordPress.org
Really Simple SSL gets your WordPress site loaded over SSL in three simple steps:
- Install and activate the plugin.
- Activate SSL in your hosting environment, or generate a free Let’s Encrypt certificate in Really Simple SSL.
- Enable SSL with One Click
Manually Update Your WordPress Site URL
If you can’t use / don’t want to use the Really Simple SSL plugin, you can do all of this manually. The next sections of this guide go through how to manually change your WordPress site’s home_url to the https:// version.
- Navigate to Settings > General in the WordPress admin.
- Update the WordPress Address (URL) and Site Address (URL) to use the
https://version. - Save settings.
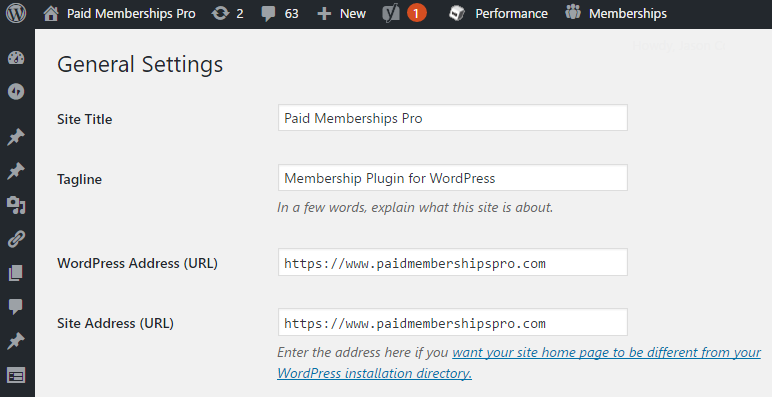
Important Note: After making this change, many things will happen. Many things may break. For starters, you will be logged out. This is because the login cookie is usually specific to the HTTP or HTTPS “version” of your page.
After WordPress is updated to use the HTTPS URL, you must login again to generate a new authentication cookie.
There are a few other issues that can come up once your site is updated to server over HTTPS. Step 4 goes over the most common ones we’ve run into.
Step 4. Fix Everything That Broke
This section documents the most common things that can break on a WordPress site when you switch to using SSL / HTTPS.
First, if you get an error message after this update, it is possible that there’s still an issue with the actual SSL certificate installed in your hosting environment.
One example may be that your site’s Apache configuration is incorrect. Make sure that you have mod_ssl installed, a valid SSL certificate, and the Apache VHOST configuration setup properly.
Redirects from the https URL to the http URL.
When you visit the https:// URL of your site, you may be redirected to the http:// version of that URL.
There are many systems that will try to force a website to use a certain “scheme” (HTTP or HTTPS). For example, if the “Force SSL” option in Paid Memberships Pro is turned on it will actually redirect away from the HTTPS version of a page for non-checkout pages. Other plugins may do similar redirects. And WordPress itself will sometimes try to force a “canonical” redirect to make sure that each page on your website has exactly one URL (this is good for SEO).
If you are using the Force SSL redirect option of PMPro or other plugins like WooCommerce, disable those features as they may interfere with your global SSL settings. You don’t need these settings for a full WordPress site served over SSL.
Users can still access the http:// version of the site.
If your site is setup to serve all pages over HTTPS, you need to redirect http:// URLs to https://. There are a few ways to do this, but we recommend adding a rule through your web server.
If you are using Apache, you can add this snippet to redirect any http traffic to the https version of the URL. Make sure to place this under your Rewrite Engine On and Rewrite Base lines:
If you are using the NGINX web server, here is the configuration you can use to redirect all HTTP traffic to HTTPS across all hosts. See Bjørn Johansen’s blog post on this topic for more details.
Pages timeout with “too many redirects” errors.
If you get a too many redirects error, what’s happening is some code somewhere is telling the browser to redirect to the HTTP version of the page. Then some other code is telling the browser to redirect to the HTTPS version of the page. What you need to do is figure out what code is trying to redirect to the HTTP version and then disable that.
Bad Plugin Settings
We’ve already mentioned that you should disable the “Force SSL” option on the payment settings page of PMPro , and PMPro should detect this anyway. Other ecommerce plugins or login/redirect plugins may have similar features that need to be disabled.
Bad PHP Server Values
Another common issue is that some hosts or proxies (like Cloudflare or Sucuri CloudProxy) can sometimes make your traffic appear to be coming over HTTP instead of HTTPS. It’s pretty subtle, but basically WordPress has a function is_ssl() that checks if the PHP value $_SERVER['HTTPS'] is set to “on”. When using a proxy, this value might be set to “off” or not set at all.
Here is some code you can add to your wp-config.php temporarily to test the $_SERVER values to see if they are setup correctly. Add this code to wp-config.php and then navigate to https:// yoursite.com/?test=1.
The output should be something like this:
Note the HTTPS value. If you are loading an HTTPS URL, but this value is set to “off”, “false”, or blank. Look for another value indicating the scheme being used. Many proxies will set the HTTP_X_FORWARDED_PROTO value and you add this code to your wp-config.php to copy that value into the HTTPS.
Bad Plugin Code
If you can’t even get into the admin to change this feature, you can disable plugins one by one by renaming the folders on the server to plugin-name-o or something similar. This will hide it from WordPress and that plugin won’t be loaded. If disabling a plugin fixes the issue, then you know that plugin is (at least partly) to blame for the redirect. You can read more about how to disable all plugins when locked out of the admin at WPBeginner here.
What to do next depends on the plugin at fault. Whether it’s PMPro, one of our Add Ons, or any other plugin, our support team will help you fix the issue. Note that sometimes these issues aren’t as straight forward as just programming things correctly the first time. Issues can arise due to conflicts between plugins, themes, or specific server settings. Be understanding with us and any plugin or theme developer you reach out to for help.
Bad Web Server Redirect Rules
Earlier in this guide we shared an example on how to redirect all traffic to the HTTPS URLs. If this redirect code is not correct or there is similar but conflicting code in your configuration, then infinite redirect loops can occur. Disable the redirect rules to see if that fixes things. Then try to figure out the correct rules for what you need.
Mixed Content Errors in WordPress Sites With SSL
When you load a web page over HTTPS, your web browser will block any content linked through an HTTP (non-secure) URL. WordPress and any properly coded plugins or themes will use “relative URLs” or otherwise attempt to detect whether a site is using SSL before outputting a URL and so will avoid this issue. However, if a URL is “hard coded” with the http:// protocol, whether in a post, stylesheet, JavaScript file, or somewhere else, these URLs will get blocked when a page is loaded over HTTPS.
You can notice mixed content errors because:
- Your page looks funny because your site isn’t loading certain stylesheets, JavaScript scripts, images, or other files.
- The green/gold/etc padlock in the upper left corner (or lower right corner) of your browser may appear red or yellow instead of green or as an ! instead of a padlock.
- The Chrome/Safari/Firefox/Firebug debug bar “Console” will show errors.
In Chrome, you can view mixed content (and other errors) in the debug tools console by holding Ctrl + Shift + J on PCs or Cmd + Option + J on Macs. Other browsers have similar features. It will look like this:

Note the “Mixed Content” error at the bottom. The error message includes the blocked resource or URL. You can use context clues in the resource URL to figure out where that bad URL is coming from.
- If the file is located within your theme, then the problem is probably in your theme.
- If the file is located within a plugin folder, then the problem is probably in that plugin.
- If the file is located within the uploads folder, you have most likely hard coded the in a post’s content.
Another common situation is saving theme settings to options, e.g. a header image. Some theme’s and plugins that save options like this save the full URL. You can save the new HTTPS URL by clearing out and reseting these options.
There are plugins that can fix most of these mixed content issues. On the PMPro payment settings page, check the “Extra HTTPS URL Filter” setting. This tells PMPro to correct any non-HTTPS URLs on the site. You can also try the Really Simple SSL plugin or the WP Force SSL plugin, which have more complicated methods of fixing mixed content errors.
If you still see errors even after activating one of the above plugins, then you’ll have to fix the issues “manually”. Please reach out to us in our member forums or reach out to the applicable plugin or theme developer. Sometimes, it’s as easy as changing a URL. Sometimes another server may be loading a resource that doesn’t serve files over HTTPS at all. In these cases, you’ll need to stop using that service or find a work around.
Summary
I hope this document helps some you start using an SSL certificate in your WordPress site. If you’re tasked with moving a site to full on HTTPS, there are many of steps to take, from choosing an SSL provider, installing the SSL certificate, and fixing any issues that arise. This post shares as much detail as possible for those that need to understand the technical details of using SSL with WordPress.
If you need help transitioning to HTTPS, we will help our PMPro customers as much as possible in our member forums (learn about our support). Be ready to involve your host or SSL provider. At the very least, we will need to get access information from you and find the time to carefully access your site to debug and fix anything we can.


